Protecting sensitive information requires rigorous oversight of external partners. A Third-Party Vendor Data Security Compliance Request ensures that service providers adhere to your organization's strict privacy standards and regulatory requirements. Establishing clear expectations mitigates cyber risks and strengthens your overall security posture during the onboarding process. To help you streamline this formal inquiry, below are some ready to use template.
Letter Samples List
- Initial Vendor Data Security Compliance Request Letter
- Annual Insurance Agency Vendor Information Security Audit Letter
- Third-Party Software Provider Cyber Security Assessment Letter
- Insurance Client Data Privacy and Protection Agreement Letter
- Vendor Network Security and Infrastructure Compliance Request Letter
- Third-Party Cloud Storage Security Certification Request Letter
- Insurance Agency Non-Public Information Vendor Acknowledgment Letter
- Vendor Incident Response and Data Breach Protocol Request Letter
- Third-Party Payment Processor Security Standards Compliance Letter
- Insurance Brokerage Vendor SOC Reporting and Verification Letter
- Regulatory Data Security Framework Compliance Request Letter
- Third-Party Vendor Access Management and Encryption Policy Letter
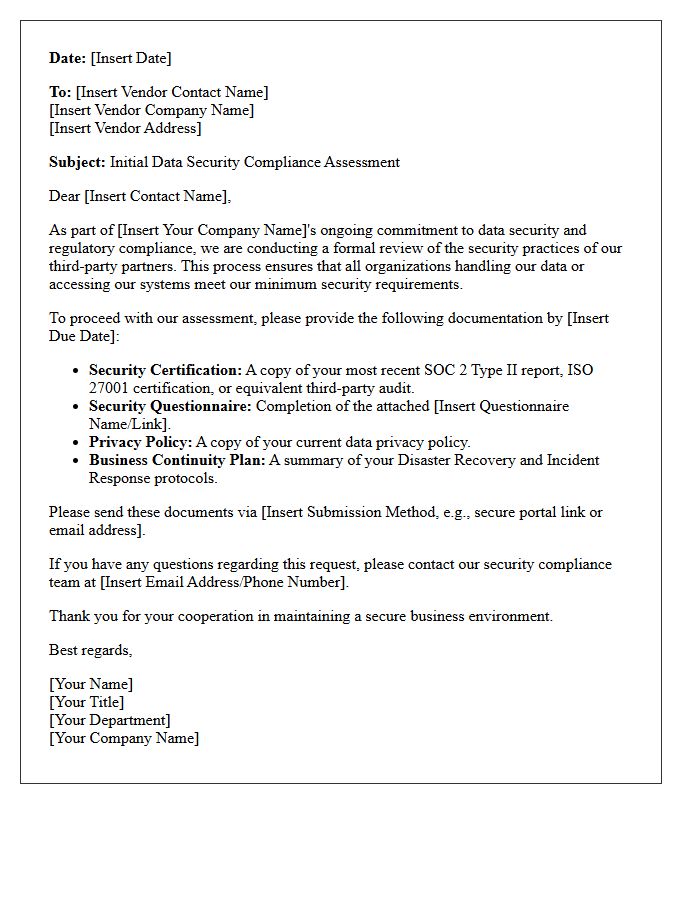
Initial Vendor Data Security Compliance Request Letter
An Initial Vendor Data Security Compliance Request Letter serves as the first step in your third-party risk management process. This formal document notifies potential partners that they must undergo a rigorous security assessment to protect your organization's sensitive information. It typically includes a Self-Assessment Questionnaire (SAQ) and requests evidence of certifications like SOC 2 or ISO 27001. Ensuring vendors meet your cybersecurity standards before signing a contract is essential for maintaining regulatory compliance and preventing costly data breaches caused by external vulnerabilities.
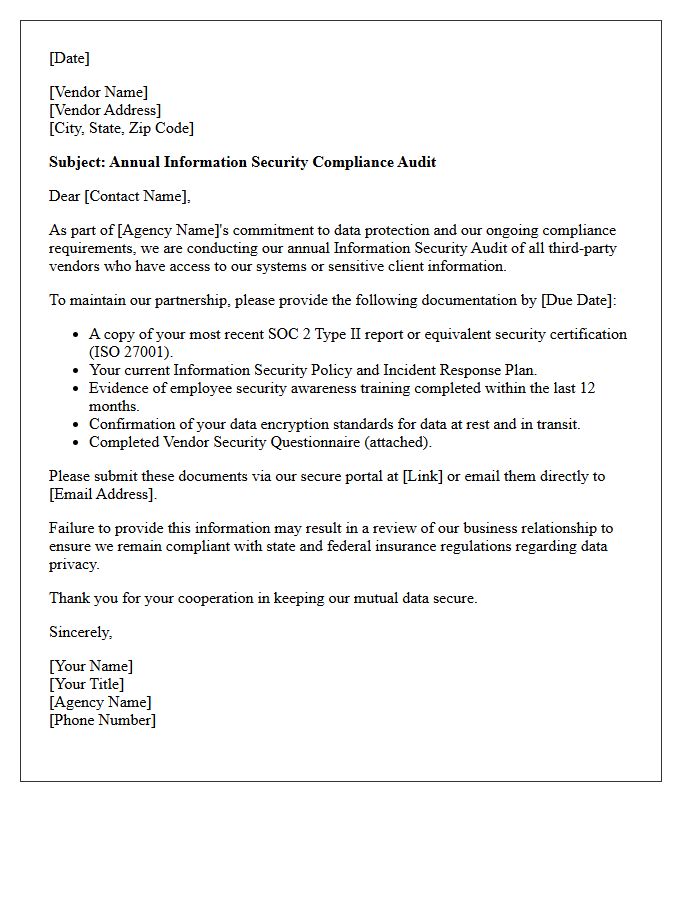
Annual Insurance Agency Vendor Information Security Audit Letter
An Annual Insurance Agency Vendor Information Security Audit Letter is a formal request used to verify that third-party partners maintain robust data protection standards. This document ensures compliance with regulations like GLBA or state-specific laws by assessing cybersecurity protocols, encryption, and risk management. Agencies must review these letters to mitigate potential liabilities and prevent unauthorized access to sensitive client policy data. Timely response and accurate documentation are essential for maintaining trust and ensuring uninterrupted operational partnerships within the insurance ecosystem.
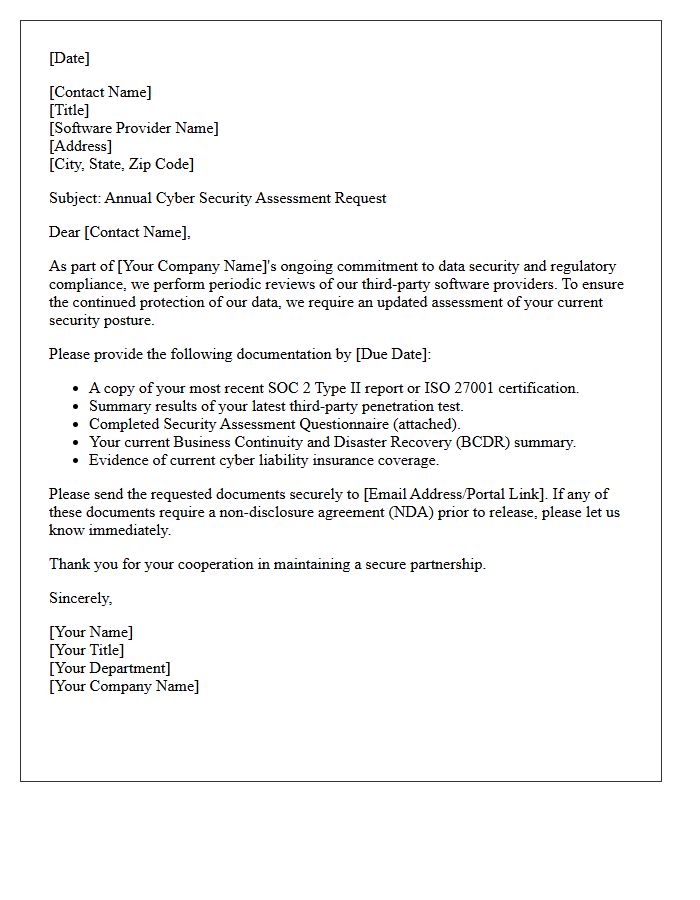
Third-Party Software Provider Cyber Security Assessment Letter
A Third-Party Software Provider Cyber Security Assessment Letter is a critical document verifying that a vendor meets specific security standards. It provides assurance to clients that the software's infrastructure, data handling, and privacy protocols have been rigorously evaluated. This letter typically summarizes findings from audits like SOC 2 or ISO 27001, highlighting risk mitigation strategies. For organizations, reviewing this assessment is essential for maintaining compliance and ensuring that external integrations do not introduce vulnerabilities into their own digital ecosystem.
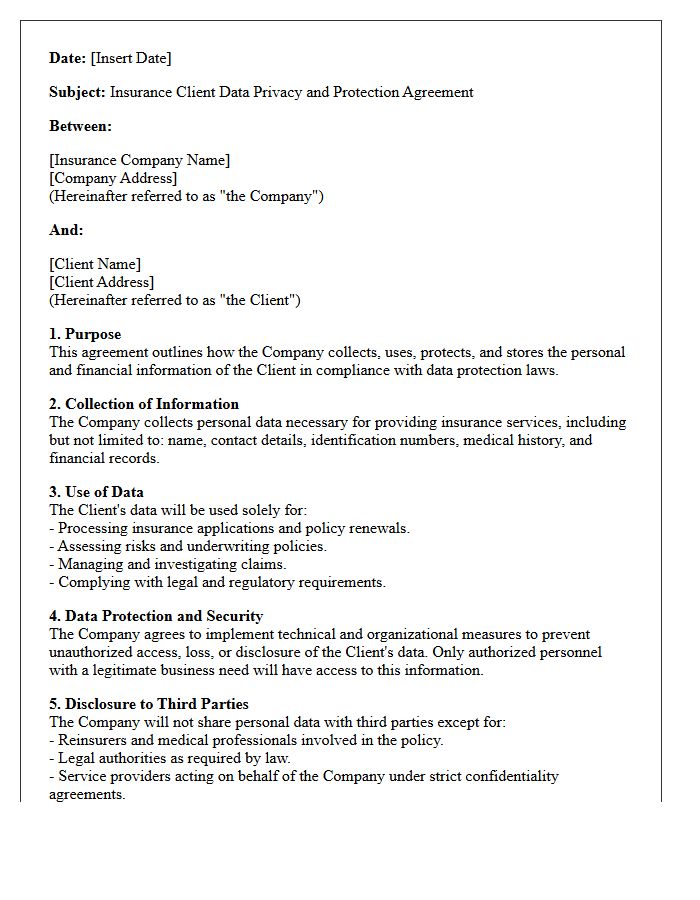
Insurance Client Data Privacy and Protection Agreement Letter
An Insurance Client Data Privacy and Protection Agreement Letter is a critical document ensuring the confidentiality of sensitive personal and financial information. It serves as a legal commitment that the insurer adheres to data protection regulations like GDPR or CCPA. This letter outlines how data is collected, stored, and shared, protecting clients from unauthorized access or breaches. By signing, both parties establish mutual trust, ensuring that private details are handled with integrity and transparency, which is essential for maintaining professional compliance and mitigating identity theft risks within the insurance industry.
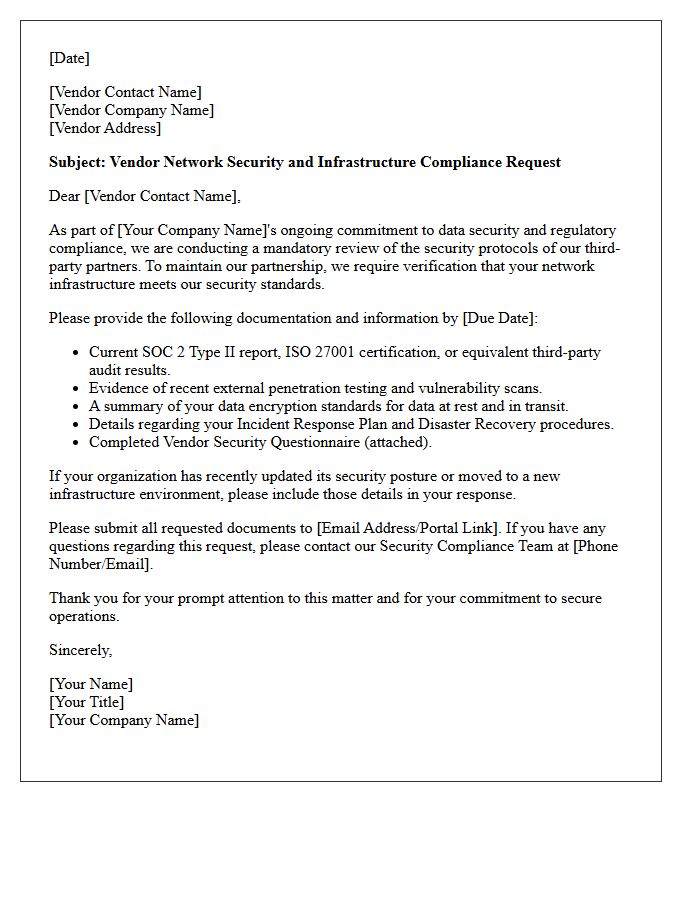
Vendor Network Security and Infrastructure Compliance Request Letter
A Vendor Network Security and Infrastructure Compliance Request Letter is a formal document used to verify a partner's technical safeguards. It ensures that third-party providers adhere to industry standards like ISO 27001 or SOC 2. By requesting proof of encryption, firewall configurations, and vulnerability management, businesses mitigate supply chain risks. This letter acts as a critical tool for due diligence, protecting sensitive data from external breaches while maintaining regulatory alignment. It establishes accountability, requiring vendors to demonstrate robust infrastructure defense before integration into your corporate ecosystem.
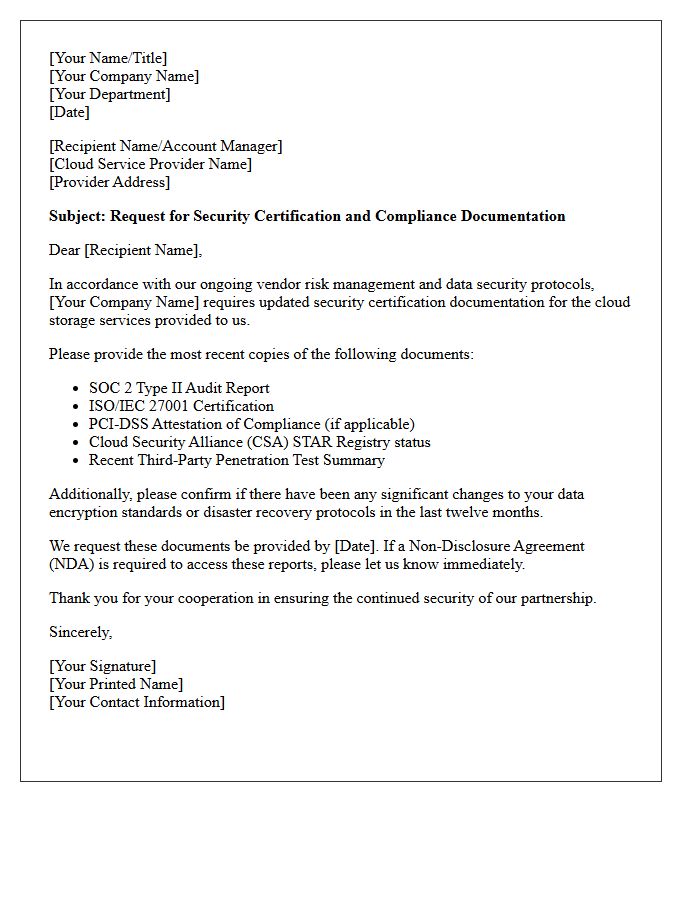
Third-Party Cloud Storage Security Certification Request Letter
A Third-Party Cloud Storage Security Certification Request Letter is a formal document used to verify a provider's compliance with industry safety standards. It is essential for risk management, ensuring that sensitive data is protected by verified protocols like ISO 27001 or SOC 2. Organizations use this request to perform due diligence before outsourcing data storage. By obtaining official certifications, businesses confirm that the cloud vendor maintains robust encryption, access controls, and incident response measures to prevent unauthorized breaches and ensure regulatory alignment.
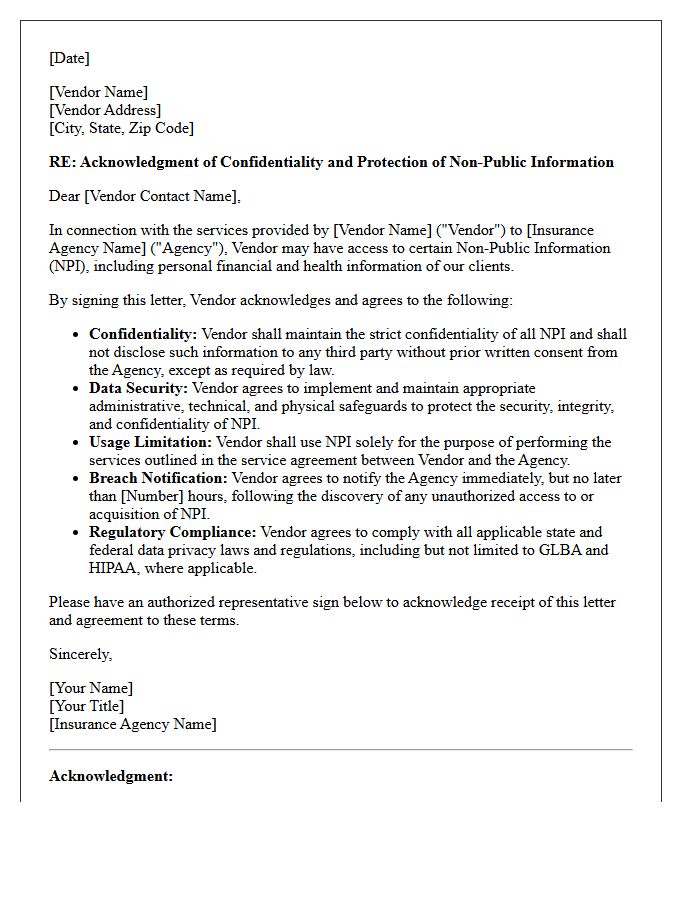
Insurance Agency Non-Public Information Vendor Acknowledgment Letter
An Insurance Agency Non-Public Information Vendor Acknowledgment Letter is a critical compliance document used to safeguard sensitive data. It ensures that third-party service providers formally agree to protect non-public personal information (NPI) in accordance with state and federal privacy regulations like GLBA. By signing, vendors acknowledge their legal obligation to implement robust security controls and maintain confidentiality. This letter mitigates liability for agencies by establishing clear standards for data handling, breach notification protocols, and the restricted use of client information, ultimately maintaining regulatory oversight and consumer trust.
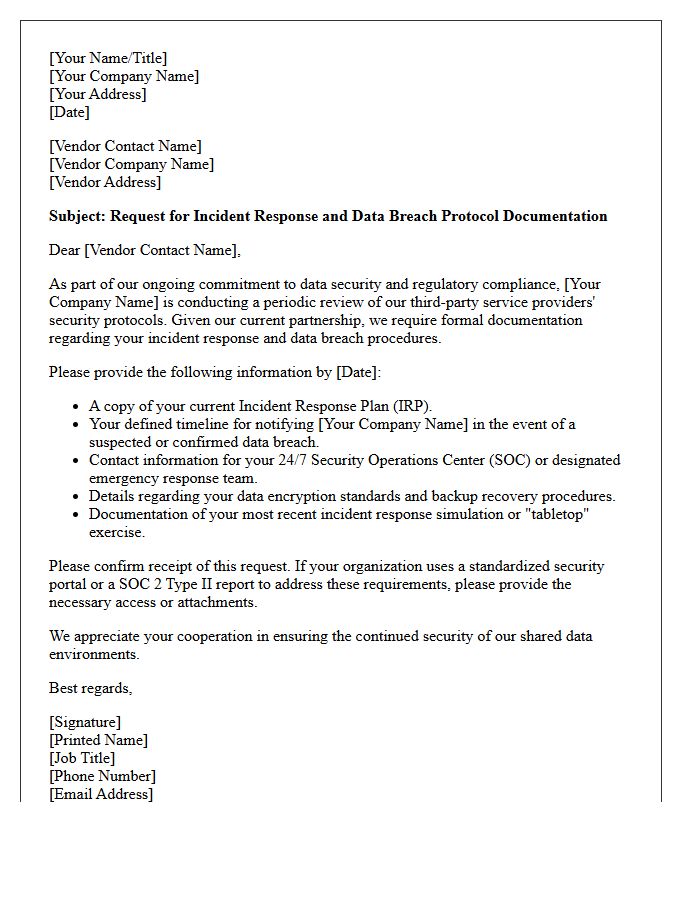
Vendor Incident Response and Data Breach Protocol Request Letter
A Vendor Incident Response and Data Breach Protocol Request Letter is a formal document used to evaluate a third-party service provider's security preparedness. It ensures that vendors have robust incident response plans and clear communication channels in the event of a security compromise. Requesting this information is vital for maintaining regulatory compliance and mitigating supply chain risks. By documenting these protocols, organizations protect sensitive data and establish accountability, ensuring that any potential data breach is identified, reported, and contained according to agreed-upon legal and operational standards.
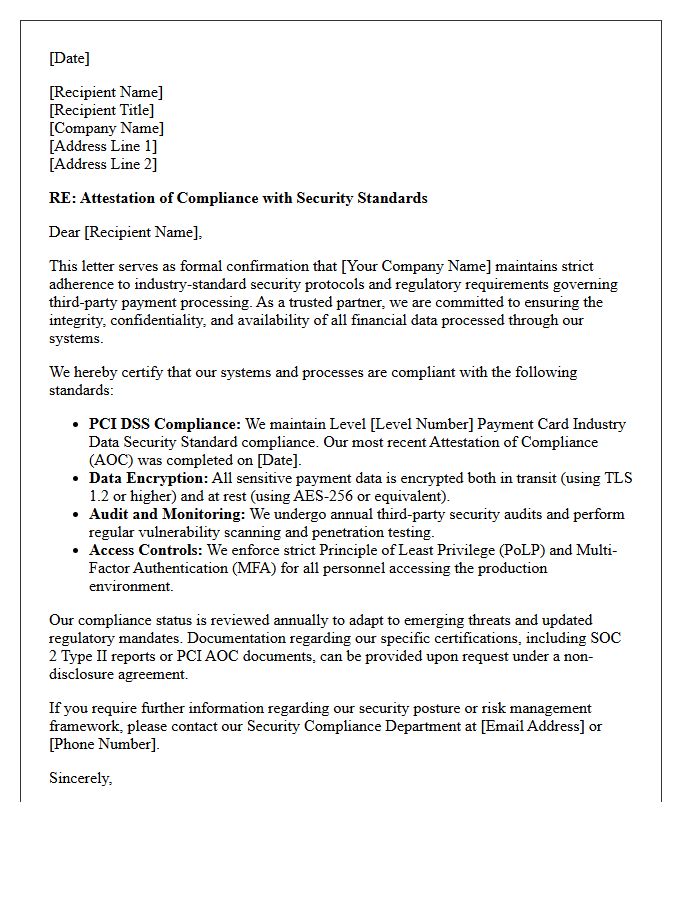
Third-Party Payment Processor Security Standards Compliance Letter
A Third-Party Payment Processor Security Standards Compliance Letter is a formal document verifying that a service provider adheres to strict PCI DSS requirements. This letter serves as essential proof for businesses that their vendor maintains secure data encryption and robust infrastructure to protect sensitive cardholder information. It minimizes liability by confirming that financial transactions are handled according to industry-mandated security protocols. Organizations must regularly review these letters to ensure their partners undergo consistent independent audits, safeguarding the entire payment ecosystem from potential data breaches and unauthorized access.
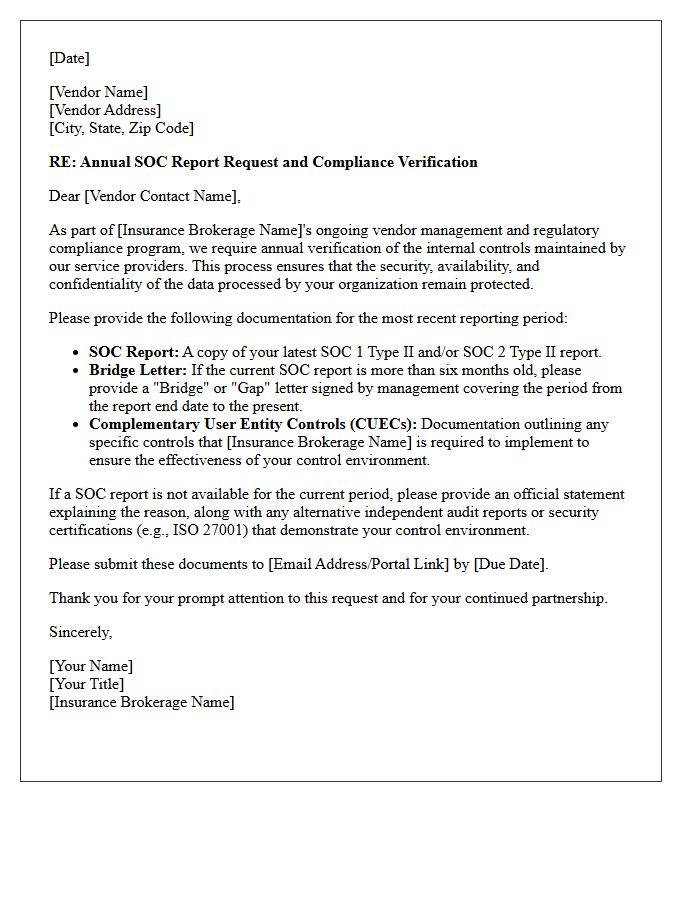
Insurance Brokerage Vendor SOC Reporting and Verification Letter
An insurance brokerage vendor must undergo regular audits to ensure data security compliance. The SOC 2 Type II report is the most critical document, providing independent verification of internal controls over a specific period. Since full reports contain sensitive details, vendors often issue a SOC Verification Letter (or Bridge Letter) to confirm continuous coverage between audit periods. This process ensures the protection of sensitive policyholder information and mitigates third-party operational risks. Carriers and clients must review these documents to verify the vendor's adherence to industry-standard security protocols.
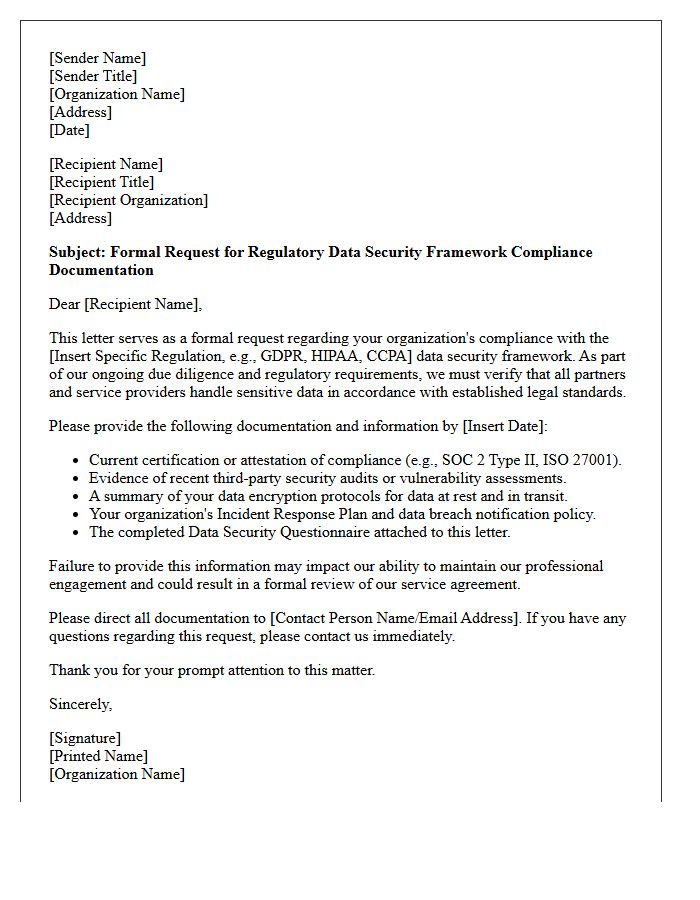
Regulatory Data Security Framework Compliance Request Letter
A Regulatory Data Security Framework Compliance Request Letter is a formal document sent to vendors or partners to verify their adherence to cybersecurity standards. This letter ensures that third parties protect sensitive information according to legal mandates like GDPR, HIPAA, or SOC2. It typically requests proof of security audits, risk assessments, and internal controls to mitigate data breaches. Receiving this request means you must demonstrate regulatory alignment to maintain business continuity and trust, as non-compliance poses significant legal and operational risks to the entire supply chain.
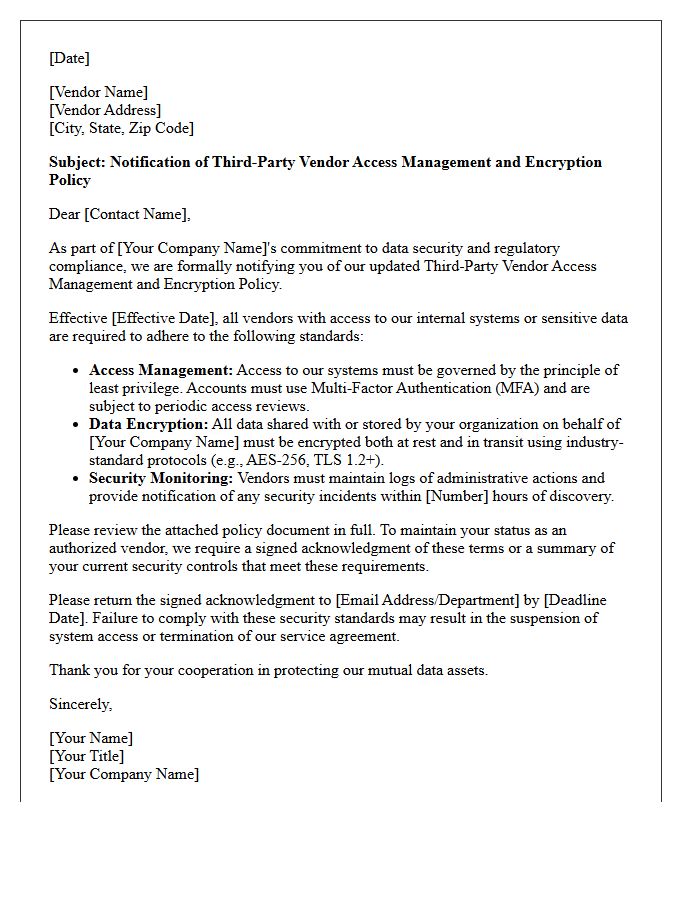
Third-Party Vendor Access Management and Encryption Policy Letter
Establishing a robust Third-Party Vendor Access Management and Encryption Policy is essential for securing organizational data. This letter mandates that all external partners strictly follow least privilege protocols when accessing internal networks. Furthermore, it enforces mandatory end-to-end encryption for all sensitive information shared or stored by vendors. By formalizing these requirements, organizations mitigate supply chain risks, ensure regulatory compliance, and prevent unauthorized data breaches. Clear communication of these security standards protects digital assets and strengthens the overall integrity of the business ecosystem against evolving cyber threats.
What is a Third-Party Vendor Data Security Compliance Request?
A Third-Party Vendor Data Security Compliance Request is a formal inquiry sent to external service providers to verify that their cybersecurity controls, data handling practices, and privacy protocols align with the hiring organization's regulatory requirements and risk management standards.
Which compliance frameworks are typically covered in a vendor security assessment?
Assessments commonly evaluate adherence to global and industry-specific standards such as SOC 2 Type II, ISO/IEC 27001, GDPR, HIPAA, and PCI DSS, depending on the nature of the data being processed and the jurisdiction of the business operations.
What documentation is required to fulfill a security compliance request?
Vendors are typically expected to provide updated SOC reports, a completed Consensus Assessments Initiative Questionnaire (CAIQ) or SIG Core/Lite, evidence of recent penetration testing, a formal Business Continuity Plan (BCP), and copies of their internal Information Security Policies.
How does third-party risk management (TPRM) protect sensitive data?
TPRM mitigates the risk of data breaches by ensuring that subcontractors and service providers maintain rigorous encryption, access controls, and vulnerability management systems, thereby preventing weak links in the supply chain from compromising the primary organization's data.
How often should a vendor's data security compliance be re-evaluated?
Compliance reviews should be conducted annually or whenever there is a significant change in the vendor's service scope, a major infrastructure migration, or the discovery of a new critical vulnerability that impacts the third-party's operational environment.

Comments